HPE NonStop and the “data-to-everything platform”
XYGATE Merged Audit (XMA), included with every HPE NonStop server since 2010, is an easy-to-use and integral security component of the HPE NonStop operating system. XMA collects data from application, system and audit logs into a single, normalized SQL database to generate reports and forward data to your log management or analytics solution. Exciting, right?
 Without having to purchase any additional software, XMA communicates directly with enterprise solutions like Splunk “…to modernize your security operations and strengthen your cyber defenses”.
Without having to purchase any additional software, XMA communicates directly with enterprise solutions like Splunk “…to modernize your security operations and strengthen your cyber defenses”.
Data is collected from EMS, Safeguard, ACI Base24, iTP Webserver, XYGATE installations and much more. This data is aggregated, filtered, formatted, and selectively forwarded in real-time. Did I mention you don’t have to try or buy any additional software? XMA is on your NonStop servers already! You own it!
Getting HPE NonStop server data to Splunk is easy. Whether your data is in native XMA/NonStop format, Common Event Format (CEF) or a custom format, it can be sent to multiple targets via TCP or UDP. The only thing to decide is which data you want to send.
XMA is installed and set up within minutes. Configuring XMA to forward data to Splunk takes even less time. All you need is the IP address, port and transport method (TCP or UDP). Pop those settings into the template inside of your XMA filters file and off you go.
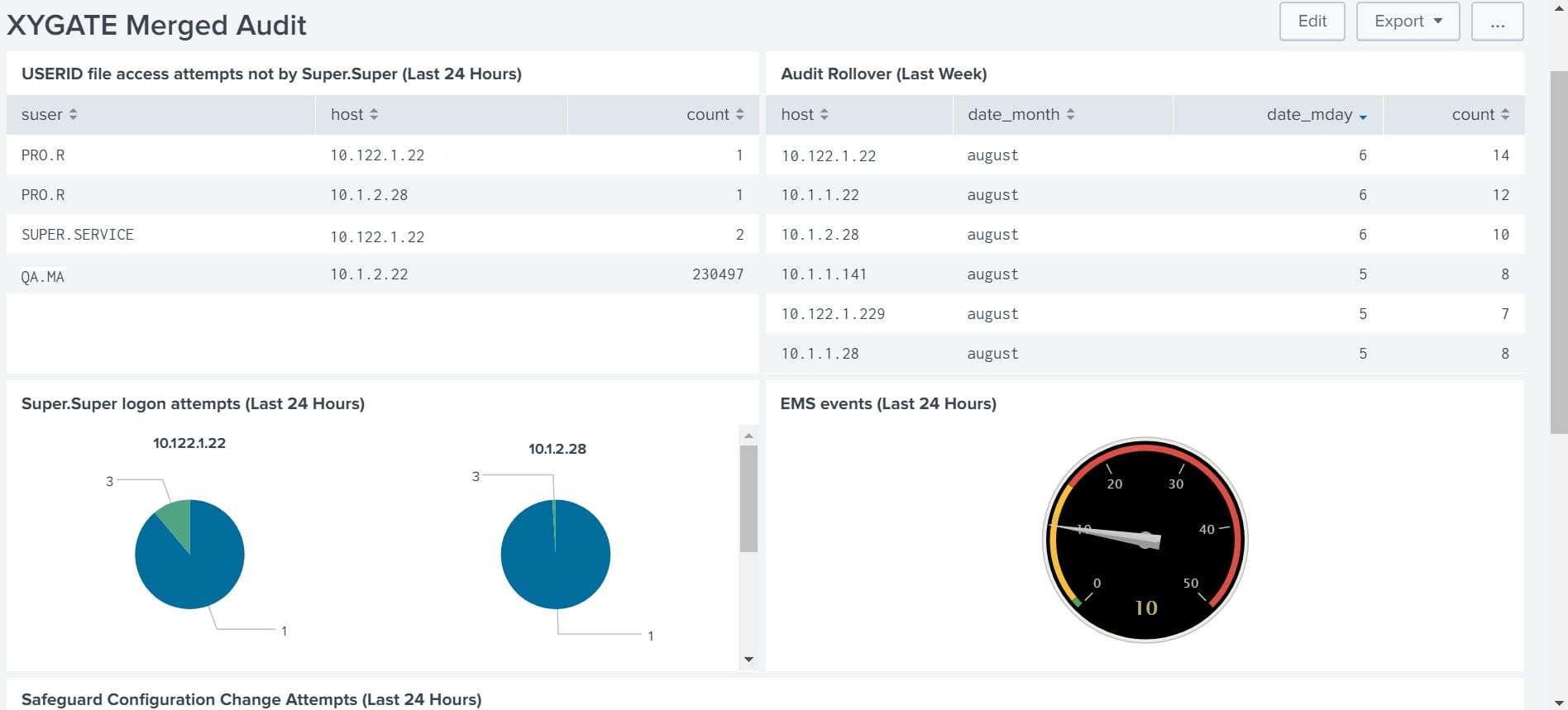
Sit back, relax, and let your SOC monitor the log data from Splunk, while you enjoy modern, intelligent, and intuitive enterprise dashboards.
Here are XYPRO’s top 5 recommended reports:
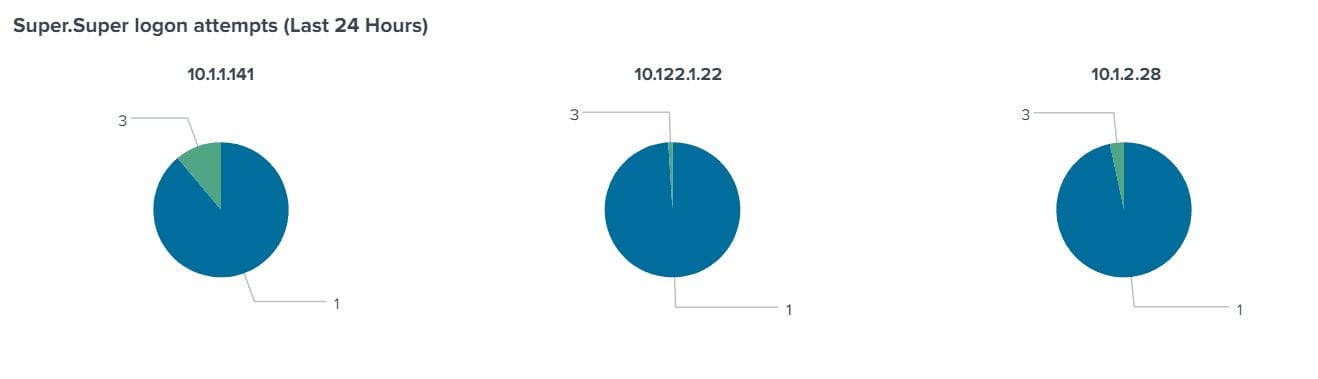
- Privileged Logons (both pass and fail). Privileged users typically have access to everything on your NonStop server. Monitoring SUPER.SUPER and other privileged logons are critical for any NonStop environment.

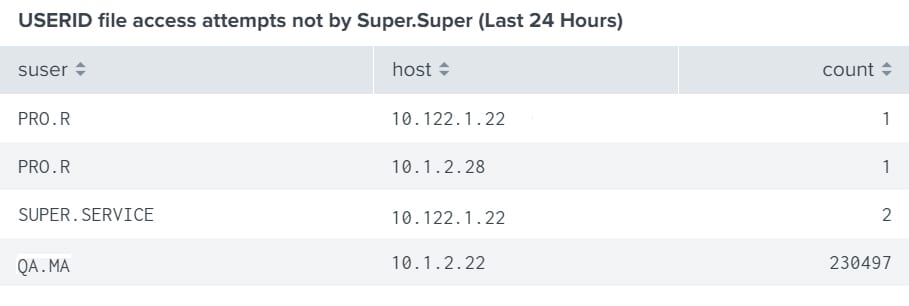
- Access to sensitive data (both pass and fail) – This includes the Safeguard USERID file and other sensitive application data and configurations files.

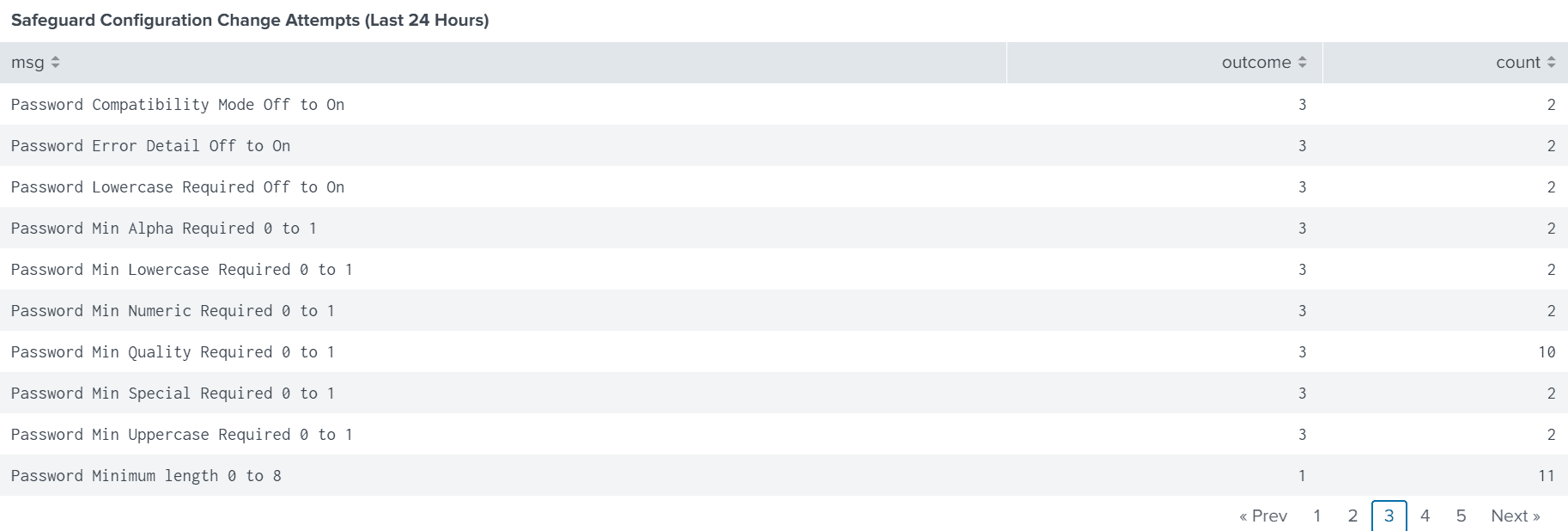
- Attempts to modify any security subsystem – This includes Safeguard Globals and other critical components that may weaken the system or put it at risk.

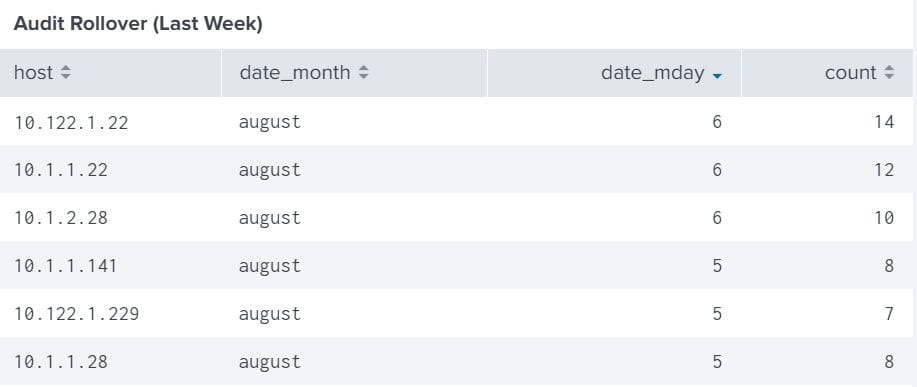
- Initialization, stopping, or pausing of audit logs – This is a critical requirement for PCI DSS 10.2.6. Audit log files are used as evidence for tracking activity or access to resources. Clearing or tampering with logs will compromise the integrity of that evidence and allow a malicious user to cover their tracks. This use case ensures Splunk can report on any activity that alters a log file.

- System integrity changes – Integrity Monitoring is a foundational requirement for security compliance frameworks to help identify unexpected or malicious activity across critical system files, diagnose unwanted or inadvertent changes, and shut down attacks before they have a chance to cause damage and disruption. If your organizations that collect and process credit card transactions and payments data must comply with the Payment Card Industry Data Security Standard (PCI DSS) requirements 10.5.5 and 11.5 that state organizations must make efforts to monitor file modifications and ensure the integrity of critical logs from within their Cardholder Data Environment (CDE).

Relieved to find the solution has been here all along? Contact your XYPRO rep for more information! Don’t miss our HPE NonStop Splunk Integration Webinar on August 26th, 2020!
Register for the webinar today! And Happy Splunk -ing!
The XYPRO Team

Steve Tcherchian, CISSP, PCI-ISA, PCIP is CEO of XYPRO Technology, a leading provider of mission-critical cybersecurity solutions that protect the digital backbone of industries worldwide. With over 20 years of experience, Steve brings a unique blend of technical expertise, strategic vision, and a customer-first approach that has transformed XYPRO into a top-tier cybersecurity provider, driving record growth and accelerated adoption of its threat detection and compliance solutions across diverse sectors.
A passionate advocate for cybersecurity, Steve is dedicated to demystifying the complexities of the industry and sharing actionable insights on global stages as a sought-after speaker. His contributions extend beyond the podium: as a former member of the ISSA CISO Advisory Council, the X9 Security Standards Committee, the Forbes Tech Council, and as a patent holder, Steve has shaped pivotal cybersecurity standards and innovations that safeguard the world’s most critical workloads.